How Secure Shield™ Works
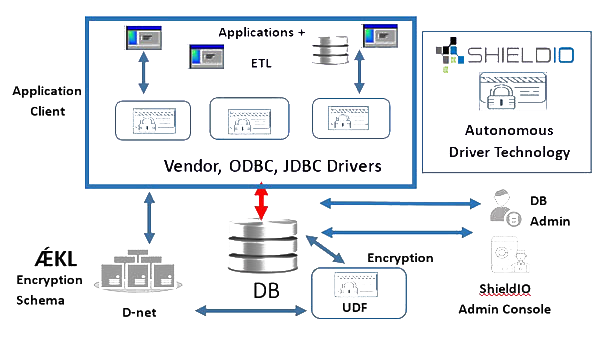
Secure Shield's™ numerous benefits are enabled by a suite of technologies developed by ShieldIO that leverage artificial intelligence, proprietary key encryption key generation libraries, autonomous drivers, distributed networks, and custom database indexing providing each database a distinctive DNA. These ShieldIO technologies enable the most resilient, scalable, easy to deploy, unintrusive, and upgradable data protection platform in the market.
The ShieldIO Foundational Technology Suite
arDra™
arDra is ShieldIO's artificial intelligence engine that is the brains behind the technology. arDra encodes each database, not just each organization, but each database with a distinctive signature that we call the Database DNA. Once the DNA is established, arDra then develops a new language for that database that is derivative of its DNA, which we call an AEKL language. Each of these languages contain over 16 million distinctive words. arDra the uses both the database DNA and the language that is created to deploy AES encryption to inbound data at the driver level as an ephemeral key, which is then used again, when the key needs to be used for decryption.brains

Autonomous Driver
ShieldIO's Autonomous Driver technology is the heart of Secure Shield. Acting as a ‘Driver’ between the applications/users/edge devices and the database, the Secure Autonomous Drivers are able to work directly on the database without requiring the calling message to be altered. The ShieldIO Driver manages the data sources, choosing which fields need to be serviced from which data source (Original or Secured). It passes the queries across to the relevant sources and when it has the results back, based on the callee having the required database/application permission(s) it will reconfigure the data results bringing all the sources together. The Driver then decrypts where possible or required and passes back to the callee a single result set.


After identifying the database DNA (DDNA), arDra creates an ÆKL based language specific to that one database only. Each new language arDra invents gives her an increased vocabulary of about 16 million new words. To arDra, each of these words is a particular method to generate an ephemeral key that can be used to encrypt, decrypt, search, modify, and perform analytics on the data. The DDNA and AEKL language is unique to every database in your organization, offering an additional layer of security.
Distributed Network (DNet)
The ShieldIO DNET is a high-availability, fault tolerant, multi-site, multi-node proprietary Hardware Security Module that stores distributed, fragmented objects such as DDNAs, DSSs, and the database AEKL and provides them upon request to within a proprietary tunneling mechanism to certain client applications for management purposes as well as any drivers embedded with arDra. No single node or site of the DNET contains even a single DDNA or DSS in its entirety.
Applying ShieldIO Secure Shield™ Technologies
ShieldIO - Effortlessley Protects your Organizations Data and Unleashes your business
Protecting Your DAta & regulatory compliance

Field Level AES 256 Encryption
Ephemeral Keys

No Key Store
Painless to Implement
Data Masking
Future Proof

Advanced User Access Controls
AI Intrusion Detection
Unleash Your Business

Multi and Hybrid Cloud Deployable
Rapidly Scalable

Zero Latency Encrypted Search

Secure Data Monetization

No Application Modifications
Low Relative Resource Requirements
Tokenization